Cyber Risk Oversight: Oracle Enterprise Vulnerabilities (Jan 2026)
Executive briefing on the Oracle January 2026 CPU. Move beyond routine maintenance to assess organizational cyber risk oversight, third-party exposure mapping, and evidence-based assurance for critical enterprise systems
CYBER & TECHNOLOGY RISK
1/27/2026
Issue summary
Oracle issued its January 2026 Critical Patch Update (CPU), a scheduled security release addressing 158 identified software vulnerabilities across Oracle products, delivered through 337 security patches, including 27 classified as critical .
Affected products include enterprise platforms commonly used for databases, business applications, and middleware, including Oracle Database, Java SE (Standard Edition), WebLogic Server, MySQL, Oracle Linux, and Oracle enterprise applications .
Oracle has confirmed that at least one vulnerability is being actively exploited, and that public exploit code exists for others. Several vulnerabilities can be exploited remotely and without authentication, meaning attackers do not require valid user credentials to compromise affected systems .
Consequences if the risk materialises
If affected systems are not remediated in a timely manner, exploitation could result in:
Regulatory and legal exposure, including mandatory breach notifications, regulatory scrutiny, and potential enforcement action.
Operational disruption, affecting core services, revenue generation, or compliance obligations.
Ransomware or extortion incidents, resulting in loss of system availability and recovery costs.
Data compromise, including unauthorised access to customer, employee, or financial data.
Loss of system control, including unauthorised changes to data or system behaviour.
These outcomes may occur without user error, due to unauthenticated attack paths identified in the update .
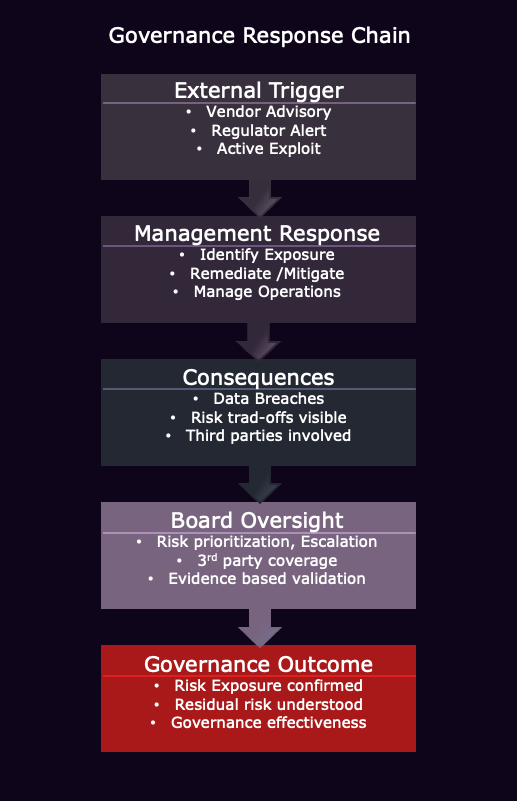
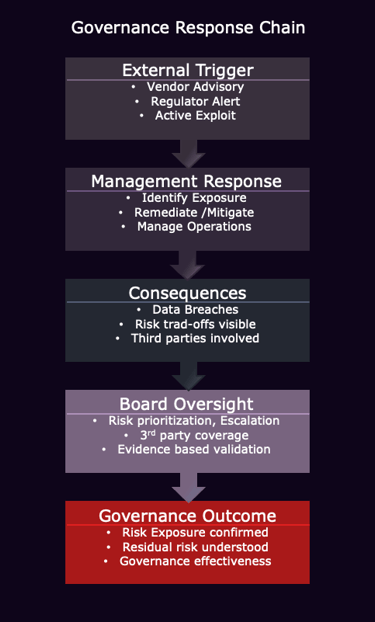
Governance significance
This matter is a risk management and assurance issue, rather than a routine technical maintenance task. Australian regulatory guidance makes clear that boards are accountable for ensuring information security controls are effective and proportionate to known threats.
APRA’s Prudential Standard CPS 234 (Information Security) requires regulated entities to identify material information security risks and ensure timely remediation, including for systems managed by third parties . ASIC has similarly emphasised directors’ responsibilities for cyber risk oversight as part of broader risk governance .
Oversight focus
The board’s interest is assurance that:
Exposure mapping: Where Oracle/Java components exist internally and via third parties.
Prioritisation: Visibility into how remediation is prioritised for internet-facing and critical systems.
Time-bound remediation: Clear timelines and escalation if deadlines slip.
Interim controls: Visibility into compensating controls applied where remediation is delayed and rationale for their use.
Verification: Evidence-based closure (not “patched” by assertion).
Third-party assurance: Confirmation from vendors/outsourcers and how it is validated.
This page provides a concise board-level summary. A full briefing is available for download.
Board Briefing
Board Posture
This briefing is provided for general board awareness and oversight framing. Issues of this nature are typically treated as “for noting with oversight”, where directors seek assurance that exposure is understood, remediation is prioritised, and completion is verified. Such events rarely require a board decision but provide a clear test of cyber risk governance effectiveness.
Contact
Reach out for briefing inquiries or support
info@theboardbriefing.com
© 2025. All rights reserved.